Cyber Security Research
Learn the basics of Cybersecurity
Cybersecurity involves protecting systems, networks, and programs from digital attacks aimed at accessing, changing, or destroying sensitive information, extorting money, or interrupting normal business processes. Implementing effective cybersecurity measures is crucial in today's digital age.
Major Issues in Cybersecurity
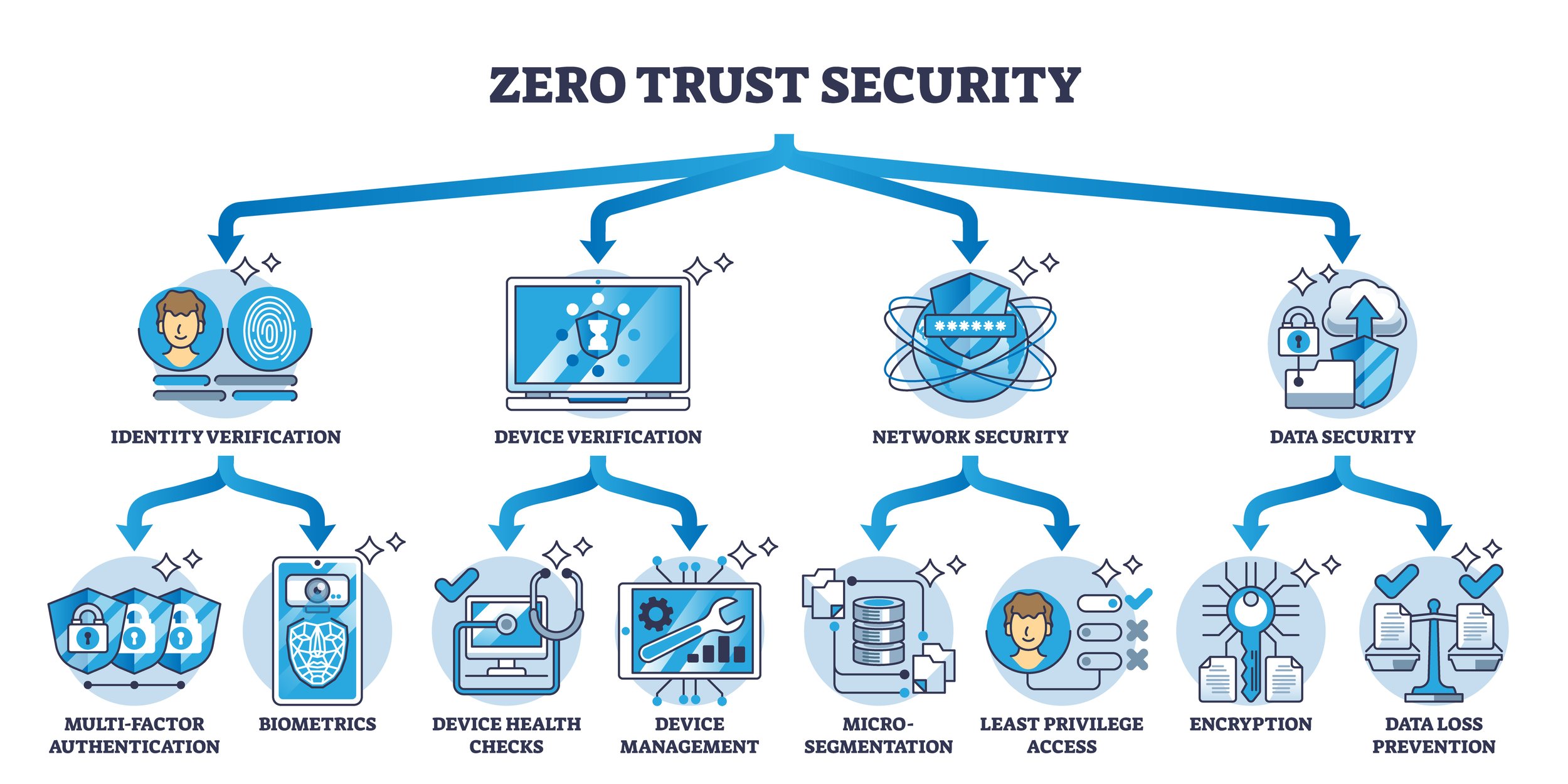
1. Zero Trust Security Zero Trust is a security framework that requires all users, whether inside or outside the organization's network, to be authenticated, authorized, and continuously validated for security configuration before being granted access to applications and data.
Principles: Never trust, always verify; enforce least privilege access.
Implementation: Use multi-factor authentication (MFA), micro-segmentation, and real-time monitoring.
Multi-Factor Authentication (MFA): Requires two or more verification factors.
2. Authentication and Identity Management Authentication and identity management ensure that users are who they claim to be and have appropriate access to systems and data.
3. Identity Theft Protection Identity theft involves stealing personal information to commit fraud. Protecting against identity theft is crucial for maintaining individual and business security.
Preventive Measures: Regular monitoring of accounts, use of strong passwords, and secure handling of personal information.
Response Strategies: Prompt reporting of suspicious activities, credit freezes, and identity theft protection services.
4. Endpoint Security Endpoint security focuses on protecting devices that connect to a network, such as laptops, smartphones, and IoT devices. It includes antivirus software, firewalls, and intrusion detection systems.
5. Network Security Network security involves measures to protect the integrity, confidentiality, and accessibility of networks and data. This includes firewalls, VPNs, and intrusion prevention systems.
6. Cloud Security Cloud security involves protecting data stored in cloud services, ensuring privacy and compliance with regulations. This includes encryption, access controls, and secure configurations.
7. Data Privacy and Protection Data privacy and protection ensure that personal and sensitive data is handled properly, complying with data protection regulations like GDPR and CCPA.
8. Incident Response and Management Incident response and management involve preparedness to respond to and recover from cybersecurity incidents effectively. This includes having an incident response plan, regular drills, and a dedicated response team.
9. Threat Intelligence Threat intelligence involves gathering and analyzing information about current and emerging threats to proactively defend against attacks. This includes monitoring threat feeds, analyzing attack patterns, and sharing intelligence with other organizations.
Single Sign-On (SSO): Allows users to log in with a single ID and password to multiple systems.
10. Evolving Technologies Cybersecurity is a constantly evolving field, with new technologies emerging to address sophisticated threats.
Artificial Intelligence (AI) and Machine Learning (ML): Used for threat detection and response automation.
Blockchain Technology: Provides secure, tamper-proof data management.
Quantum Cryptography: Offers unbreakable encryption methods for secure communication.
Conclusion
Effective cybersecurity is essential for protecting sensitive information and ensuring the smooth operation of business processes. At ITechnology, we stay at the forefront of cybersecurity advancements, researching and implementing the latest technologies to provide robust security solutions. Our goal is to safeguard businesses against evolving cyber threats, ensuring a secure and resilient digital environment.